In the 70s, mathematicians and computer scientists invented computation methods, complex for humans, but relatively simple (we’ll come back to this) for computers and other programmable devices. What we call a “hash” or hash function, can be summarized in a very simple way.
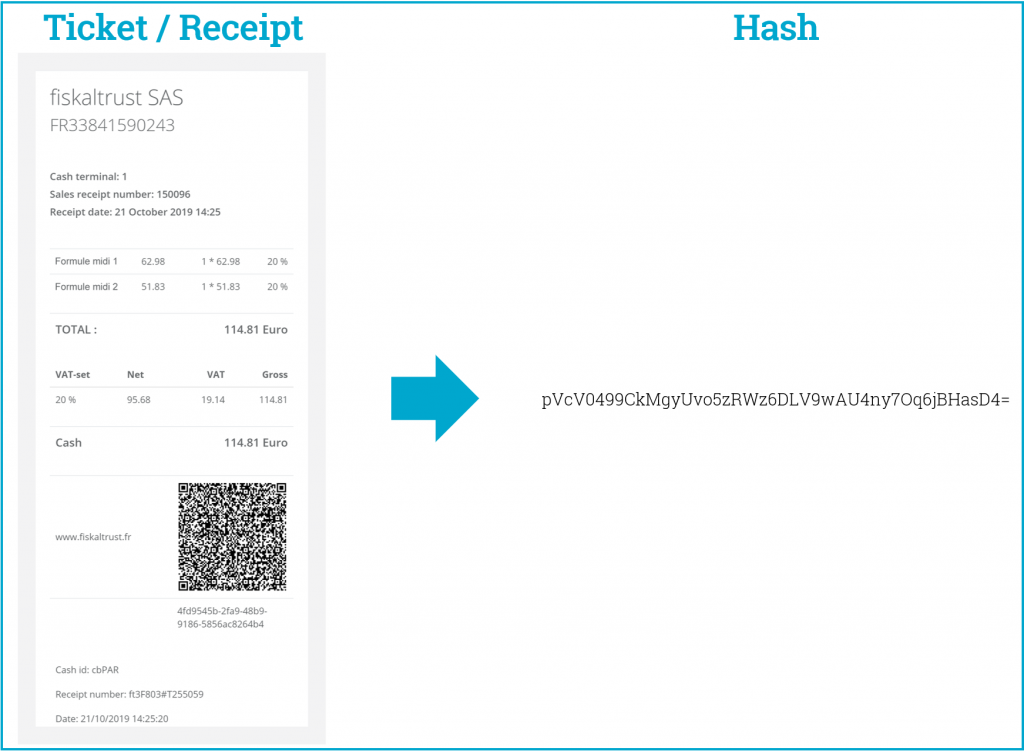
- We enter a very large item (an image, a computer program, the content of your cash register receipt, etc…) and we get an “imprint” output, for example a short text of 512 characters (for a computer that’s short!)
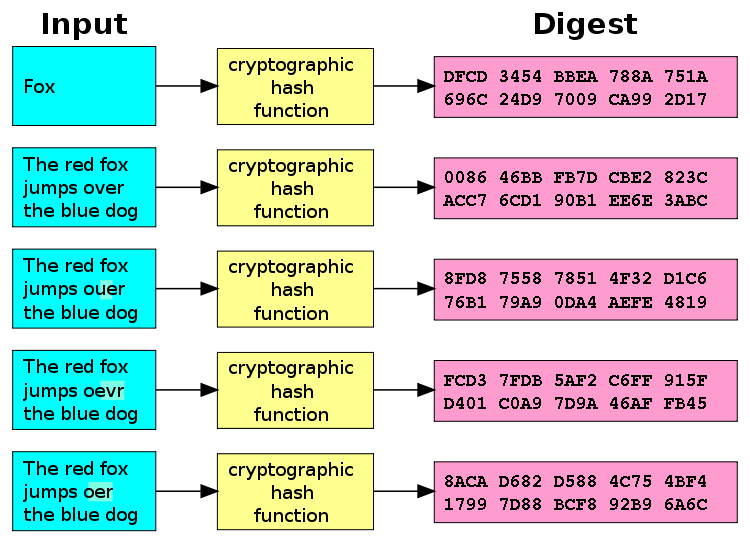
- If we provide exactly the same input element, we get exactly the same result each time. Phew!
- If we change a single detail of the input data, the output is completely different.
- An imprint of 512 characters (technically called “hexadecimal”) leaves billions of billions of different possibilities: a 1 followed by 2500 digits, creates several times more possibilites than the number of stars in the universe or the number of grains of sand on the Earth.
- So, by linking the two previous points, it is most unlikely that during your lifetime the hash of 2 different inputs will produce the same result.
- And above all, it’s a one-way street! For any given hash result, you can not determine what the input was all by itself. It’s simple for a computer, in a sense, but it would require millions of computers to continuously test all possibilities for several decades to decode one and only one hash!
Examples? In a technical or legal document, you may have heard of MD5, SHA1, SHA2, …
What is it for technically?
It verifies that nothing has been changed:
- If we change one small detail on the receipt and redo the hash, it will give a completely different result and we will know that the receipt has been changed.
- If nothing has changed, redoing the hash will give the exact same result and we will know that we have the correct hash and that the contents of the receipt have not been modified.
What is the practical objective?
A hash is used to compress files such as zip files, as the zip contains the hash of the original content. When we decompress the file, we recalculate the hash. If it’s different from the original, there is a problem… The exact problem we do not know, but it’s good to know that there is a problem!
It is used to communicate between computers. A computer never sends information without sending an additional item (it can be a hash, but it can also be much simpler). The computer that receives the communication and the additional element recalculates: if the information is different than expected, it automatically asks to send the same communication again.
This method is also used for the blockchain, password logins, the inalterability of the tax justifications requested by the French law “to fight against VAT fraud”, the electronic signature, the storage of data in short or long term, etc.
It’s used for something we call chaining and we’ll come back to that in a future article…
fiskaltrust is a partner you can trust! As a member of the NF RGPD Software and Club Access (leading the reflection on the NF 525 standard) committees, we put our expertise at your service so that you can focus on the heart of your business.
Contact us now!
Call us on +33 (0) 1 70 99 53 53 or send an e-mail to contact@fiskaltrust.fr
We look forward to discussing with you the solutions that fiskaltrust offers to help your business.